The Great Encryption Standoff: From Politics to Practice
TL;DR
France and Germany are pushing for encryption backdoors, but any “lawful access” key would also be a hacker’s key.
EU regulations (NIS2, DORA, Data Act, CRA, etc.) are simultaneously demanding stronger, state-of-the-art encryption.
The contradiction is obvious: governments talk about weakening crypto, while regulators fine companies that don’t strengthen it.
New cryptographic methods — FHE + ZKP — offer the only sustainable way forward: compliance without compromise.
Businesses that adopt these tools will stay compliant, protect data sovereignty, and earn customer trust. Those that don’t will face penalties and breaches.
The Political Flashpoint
France and Germany are pressing hard for “lawful access” to encrypted messaging apps such as Signal and WhatsApp. In plain terms, that means backdoors. For law enforcement, it’s framed as a necessary tool against serious crime. For cybersecurity experts, it’s a red flag: a universal key that criminals, foreign intelligence services, or rogue insiders could exploit the moment it exists.
Encryption doesn’t distinguish between “good guys” and “bad guys.” Create a weakness, and you’ve created a vulnerability for everyone. Businesses depending on customer trust, and citizens depending on digital safety, have reason to see this as more than a policy dispute — it’s a direct challenge to the security foundations of Europe’s digital economy.
The Regulatory Squeeze
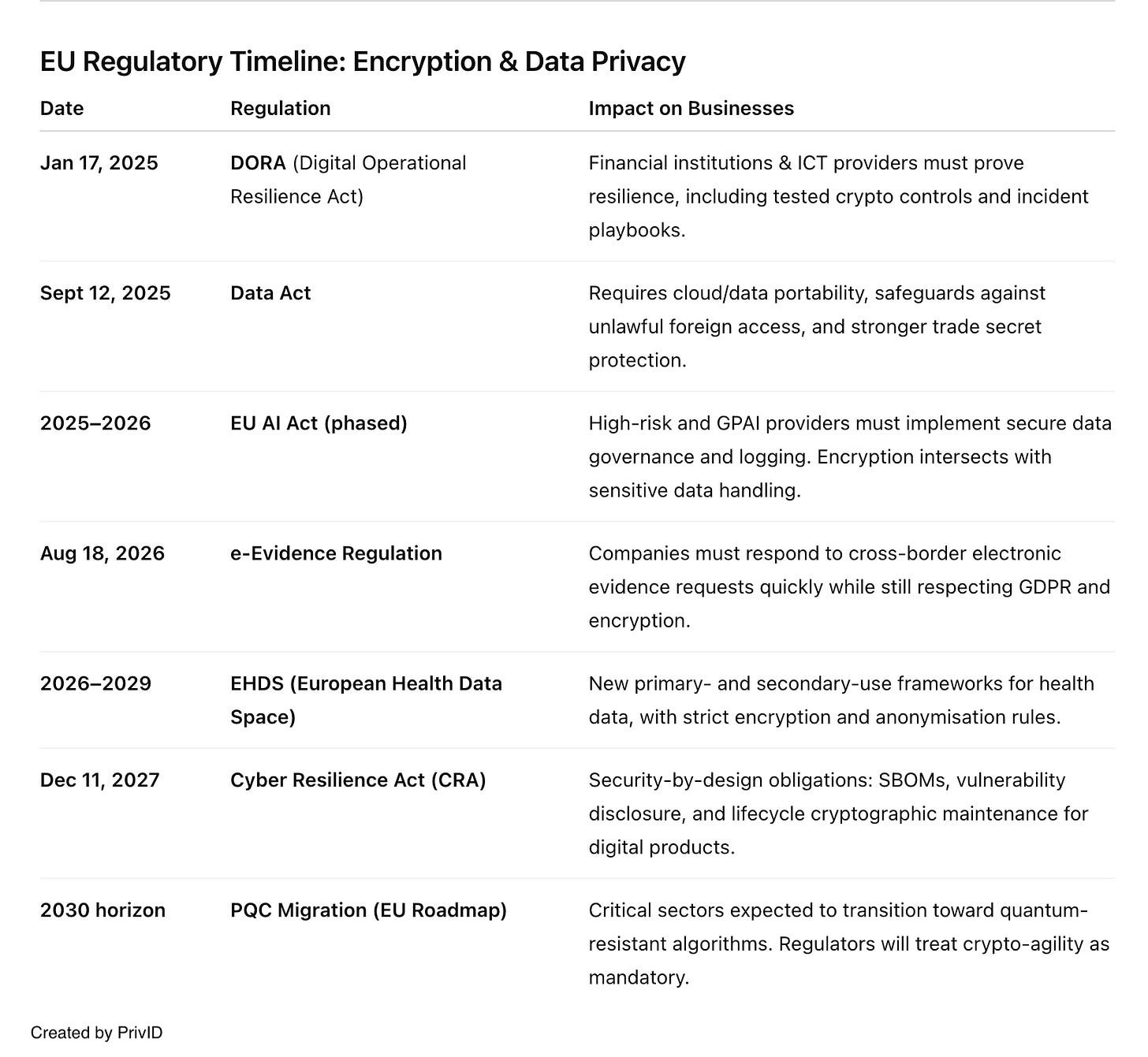
At the same time, the EU is rolling out a regulatory landscape that demands stronger, not weaker, cryptography. Here’s where businesses need to pay attention:
NIS2 (with Implementing Reg. 2024/2690):
Expands obligations to critical and “important” sectors, including cloud, data centres, MSPs, and platforms. Requires documented crypto policies, incident reporting within 24 hours, and proof that encryption is “state of the art.” Audits will check key lifecycles, algorithm choices, and your ability to adapt to new threats.DORA (live since Jan 2025):
For financial institutions and their ICT providers. Mandates tested incident playbooks, concentration risk controls, and adversarial resilience testing. Encryption practices are part of how regulators will judge operational robustness.Data Act (applies Sept 2025):
Gives users access to data generated by connected products and makes cloud switching enforceable. Providers must support portability and prevent unlawful non-EU access. That means robust encryption, secure APIs, and transparent contractual safeguards.e-Evidence Regulation (applies Aug 2026):
Enables faster cross-border orders for electronic evidence. Companies will need to respond quickly while still respecting GDPR and encryption guarantees. Backdoors aren’t required, but the pressure on lawful access workflows will grow.Cyber Resilience Act (main duties by Dec 2027):
Introduces security-by-design obligations for “products with digital elements.” That includes mandatory vulnerability reporting, software bills of materials, and long-term cryptographic maintenance.Sector-specific frameworks:
EHDS (European Health Data Space): Creates new rules for health data portability and secondary use, with strict encryption and anonymisation standards.
EU AI Act: For high-risk and general-purpose AI, requires secure data governance and logging, intersecting with encryption when handling sensitive data.
Post-quantum cryptography:
The Commission is signalling a 2030 deadline for critical sectors to move toward quantum-resistant algorithms. Organisations need crypto-agility and hybrid approaches now to avoid a last-minute scramble.
Overlay all this with the CSAM scanning proposal (potentially forcing client-side scanning of encrypted apps), and you see the pattern: regulatory demands are rising at the same time governments are floating measures that would undermine the very tools companies are required to use.
A Practical Middle Path
The standoff doesn’t need to be binary. New cryptographic methods can satisfy regulatory needs without breaking encryption:
Fully Homomorphic Encryption (FHE): Enables computations on encrypted data. Think fraud detection, statistical analysis, or compliance checks performed without ever decrypting raw content.
Zero-Knowledge Proofs (ZKP): Allow verification of a claim — “this transaction meets KYC rules,” “this user is over 18” — without revealing the underlying data.
Combined, they deliver:
Complete data protection — processing without exposure.
User control — data access remains in the hands of the individual or organisation.
Local jurisdiction — encryption ensures EU data stays subject to EU law, not foreign surveillance.
Regulatory alignment — auditors and supervisors get proof of compliance without needing decryption keys.
What It Means for Businesses
For companies operating in Europe, three points are clear:
Backdoors are not “state of the art.” Under NIS2 and DORA, deliberately weakening encryption would put you out of compliance.
Crypto-agility is mandatory. With post-quantum deadlines on the horizon, you need to know what you’re using, where, and how to replace it. Regulators will expect an inventory and a plan.
Privacy and sovereignty are market differentiators. Customers and regulators alike will gravitate to providers who can prove security without compromise.
The Bigger Picture
Europe’s encryption debate isn’t just about technology — it’s about values. The choice is whether to protect privacy and digital sovereignty with stronger cryptography, or to trade it away for the illusion of safety through backdoors.
For businesses, the opportunity is clear: those who adopt advanced encryption methods now will not only stay compliant, they’ll earn trust in a marketplace that’s increasingly defined by data protection. Those who wait will face audits, penalties, and reputational damage when the inevitable breach occurs.
The standoff is real. But the tools to move beyond it are already here.



Great article. I think implementing ZK on a Zero Trust based environment could be a winner.